Μια κακόβουλη επίθεση malware έχει εξαπολυθεί με σκοπό να χακάρει τους χρήστες του YouTube και του Facebook, εγκαθιστώντας τον information stealer S1deload Stealer που κλέβει δεδομένα και τα credentials σύνδεσης στα μέσα κοινωνικής δικτύωσης, προτού χρησιμοποιήσει τον υπολογιστή σας για να εξορύξει cryptocurrency. Να είστε σε επιφυλακή αν έχετε λογαριασμό σε οποιονδήποτε από τους δύο ιστότοπους!
Δείτε επίσης: Έχουν αυξηθεί οι κυβερνοεπιθέσεις με στόχο το firmware των Android smartphones

Η ομάδα Advanced Threat Control (ATC) της Bitdefender ανακάλυψε το νέο κακόβουλο λογισμικό και το ονόμασε S1deload Stealer λόγω της εμπειρίας του να χρησιμοποιεί DLL sideloading για να παραμένει μεταμφιεσμένο.
Από τον Ιούλιο έως τον Δεκέμβριο του 2022, τα προϊόντα της Bitdefender εντόπισαν πάνω από 600 διαφορετικούς χρήστες που είχαν μολυνθεί με αυτό το κακόβουλο λογισμικό, σύμφωνα με τον Dávid Ács από την ερευνητική ομάδα της Bitdefender.
YouTube
Ζωή Κωνσταντοπούλου: Καταιγιστικές εξελίξεις για τον Alexander Vinnik
12o Infocom Security 2022 - Παρουσιάσεις και συνεντεύξεις
Ζωη Κωνσταντοπούλου: Εξελίξεις στο ΣΤΕ για τον Mr Bitcoin
Giannis Andreou LIVE : Crypto, NFT, Metaverse προβλέψεις
LIVE: GoldDigger credential detection & PinataHub platform
LIVE : SocialTruth project - Το σύστημα εντοπισμού fake news
Δείτε επίσης: Fake ChatGPT apps/sites διανέμουν Windows & Android malware
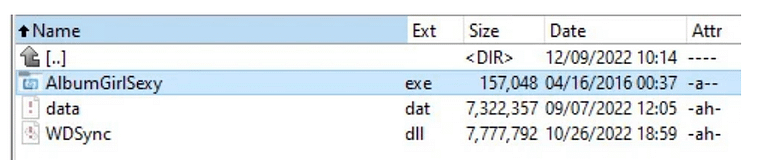
Τα θύματα εξαπατούνται ώστε να μολυνθούν χρησιμοποιώντας social engineering και σχόλια σε σελίδες του Facebook που προωθούν αρχεία με θέματα για ενηλίκους (π.χ. AlbumGirlSexy.zip, HDSexyGirl.zip, SexyGirlAlbum.zip και άλλα).
Εάν ο χρήστης πραγματοποιήσει λήψη ενός από τα συνδεδεμένα αρχεία, θα λάβει ένα εκτελέσιμο αρχείο υπογεγραμμένο με έγκυρη ψηφιακή υπογραφή Western Digital και ένα κακόβουλο DLL (WDSync.dll) που περιέχει το τελικό payload.
Αφού αποκτήσει πρόσβαση στις συσκευές των θυμάτων, ο S1deload Stealer μπορεί να καθοδηγηθεί από τους χειριστές του μέσω ενός command-and-control (C2) server για να προβεί σε οποιαδήποτε από διάφορες ενέργειες.
Όπως ανακάλυψε το Bitdefender, μπορεί να κατεβάσει και να εκτελέσει πρόσθετα components, συμπεριλαμβανομένου ενός “headless Chrome web browser” που εκτελείται στο παρασκήνιο και μιμείται την ανθρώπινη συμπεριφορά για να αυξήσει τεχνητά τον αριθμό προβολών σε βίντεο YouTube και αναρτήσεις στο Facebook.
Σε άλλα συστήματα, μπορεί επίσης να αναπτύξει ένα stealer που αποκρυπτογραφεί και εξάγει τα αποθηκευμένα credentials και τα cookies από το πρόγραμμα περιήγησης του θύματος και τη βάση δεδομένων Login Data SQLite ή έναν cryptojacker που θα εξορύξει κρυπτονομίσματα BEAM.
Εάν καταφέρει να κλέψει έναν λογαριασμό στο Facebook, το κακόβουλο λογισμικό θα προσπαθήσει επίσης να εκτιμήσει την πραγματική του αξία αξιοποιώντας το Facebook Graph API για να ανακαλύψει εάν το θύμα είναι ο διαχειριστής μιας σελίδας ή ομάδας στο Facebook, εάν πληρώνει για διαφημίσεις ή είναι συνδεδεμένος σε έναν λογαριασμό διαχειριστή επιχείρησης.
Δείτε επίσης: Google Bug Bounty: Το 2022 δόθηκαν $ 12 εκατ. σε ερευνητές
Για να προστατευτείτε από κακόβουλα προγράμματα και να διαφυλάξετε τους λογαριασμούς σας στα μέσα κοινωνικής δικτύωσης, δεν πρέπει ποτέ να εκτελείτε αρχεία από ύποπτες πηγές και να διατηρείτε πάντα την τελευταία έκδοση του anti-malware software.
Πηγή πληροφοριών: bleepingcomputer.com