By Sergiu Gatlan April 30, 2020 02:21 PM 0

A new banking Trojan can steal financial information from Android users across the United States and several European countries, including the UK, Germany, Italy, Spain, Switzerland, and France.
Dubbed EventBot by researchers at Cybereason Nocturnus who discovered it in March 2020, the malware is a mobile banking trojan and infostealer designed to abuse the Android operating system's accessibility features to steal sensitive financial data.
"EventBot targets users of over 200 different financial applications, including banking, money transfer services, and crypto-currency wallets," the Cybereason Nocturnus researchers found.
 Top ArticlesBugs in WordPress plugins for online courses let students cheat
Top ArticlesBugs in WordPress plugins for online courses let students cheat
 READ MORE
READ MORE
"Those targeted include applications like Paypal Business, Revolut, Barclays, UniCredit, CapitalOne UK, HSBC UK, Santander UK, TransferWise, Coinbase, Paysafecard, and many more." — the full list of targeted Android apps is available here.
At the moment, the malware is not being distributed via the Google Play Store, with its creators most likely using shady APK hosting websites and rogue APK marketplace for distribution to potential victims' devices.
 Apps targeted by EventBot (Cybereason Nocturnus)
Apps targeted by EventBot (Cybereason Nocturnus)
Permissions for everything
Once the targets download EventBot on their devices and start the installation process, the malware will ask to be granted a large set of permissions including the capability to run in the background, to ignore battery optimizations, and to prevent the processor from sleeping or the device from dimming the screen.
EventBot also asks to get access to Android's accessibility services which allows it to "operate as a keylogger and can retrieve notifications about other installed applications and content of open windows" once the permissions are granted.
The banking trojan also asks for permission to launch itself after system boot as a simple way to gain persistence on infected devices and run in the background as a service.
It will also request permission to read and receive SMS messages malware, thus gaining the ability to read text messages and steal one-time passcodes (OTPs) it later uses to bypass two-factor authentication (2FA) for accounts using SMS-based 2FA — EventBot also uses webinjects to circumvent 2FA.
EventBot collects the list of installed apps on the Android devices it infects, together with device info like OS and model, data that gets sent to its command-and-control server to be later harvested by its operators.
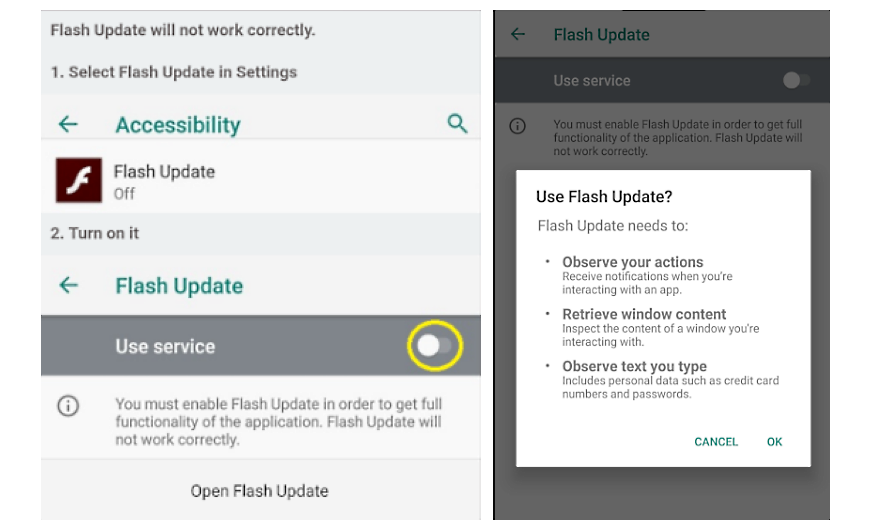 EventBot requesting permissions (Cybereason Nocturnus)
EventBot requesting permissions (Cybereason Nocturnus)
Still in development but already a threat
Although it is currently in its early stages of development, EventBot can become a major Android malware threat since it is already capable of targeting hundreds of financial apps and the developers add more new feature in each version like encryption, dynamic library loading, and automatic adjustment to device models and locales.
Because the threat actor behind this malware updates it every few days, it's just a matter of time until it catches up to other highly dangerous Android trojans like Cerberus, Anubis, and xHelper.
For instance, EventBot's developers added a layer of obfuscation in the latest version, "perhaps taking the malware one step closer to being fully operational," according to the researchers.
To defend against an EventBot infection you should avoid third-party marketplaces if possible and always install apps only from the Google Play Store as they go through a vetting process that makes sure that most potentially malicious apps are rejected.
"Cybereason believes EventBot could be the next influential mobile malware because of the time the developer has already invested into creating the code and the level of sophistication and capabilities is really high," Cybereason Head of Threat Research Assaf Dahan said.
"By accessing and stealing this data, Eventbot has the potential to access key business data, including financial data. Mobile malware is no laughing matter and it is a significant risk for organizations and consumers alike."
EventBot indicators of compromise (IOCs) including malware sample hashes, and IP addresses and domains of its command and control servers, are available at the end of Cybereason Nocturnus' report.
Starting last month, the TrickBot gang has also begun using a malicious Android app dubbed TrickMo that steals transaction authentication numbers (TANs) — including one-time passwords (OTP), mobile TAN (mTAN), and pushTAN authentication codes — to bypass the 2FA protection used by various banks

A new banking Trojan can steal financial information from Android users across the United States and several European countries, including the UK, Germany, Italy, Spain, Switzerland, and France.
Dubbed EventBot by researchers at Cybereason Nocturnus who discovered it in March 2020, the malware is a mobile banking trojan and infostealer designed to abuse the Android operating system's accessibility features to steal sensitive financial data.
"EventBot targets users of over 200 different financial applications, including banking, money transfer services, and crypto-currency wallets," the Cybereason Nocturnus researchers found.
 Top ArticlesBugs in WordPress plugins for online courses let students cheat
Top ArticlesBugs in WordPress plugins for online courses let students cheat READ MORE
READ MORE"Those targeted include applications like Paypal Business, Revolut, Barclays, UniCredit, CapitalOne UK, HSBC UK, Santander UK, TransferWise, Coinbase, Paysafecard, and many more." — the full list of targeted Android apps is available here.
At the moment, the malware is not being distributed via the Google Play Store, with its creators most likely using shady APK hosting websites and rogue APK marketplace for distribution to potential victims' devices.
 Apps targeted by EventBot (Cybereason Nocturnus)
Apps targeted by EventBot (Cybereason Nocturnus)Permissions for everything
Once the targets download EventBot on their devices and start the installation process, the malware will ask to be granted a large set of permissions including the capability to run in the background, to ignore battery optimizations, and to prevent the processor from sleeping or the device from dimming the screen.
EventBot also asks to get access to Android's accessibility services which allows it to "operate as a keylogger and can retrieve notifications about other installed applications and content of open windows" once the permissions are granted.
The banking trojan also asks for permission to launch itself after system boot as a simple way to gain persistence on infected devices and run in the background as a service.
It will also request permission to read and receive SMS messages malware, thus gaining the ability to read text messages and steal one-time passcodes (OTPs) it later uses to bypass two-factor authentication (2FA) for accounts using SMS-based 2FA — EventBot also uses webinjects to circumvent 2FA.
EventBot collects the list of installed apps on the Android devices it infects, together with device info like OS and model, data that gets sent to its command-and-control server to be later harvested by its operators.
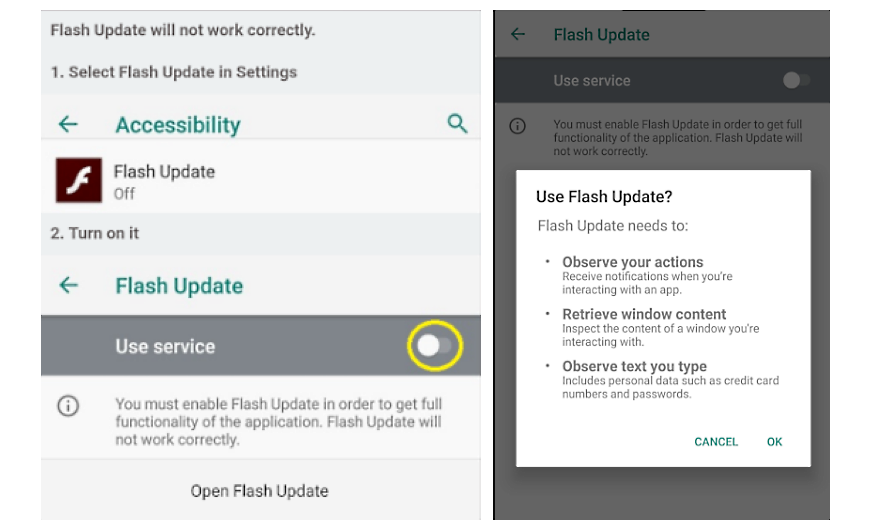 EventBot requesting permissions (Cybereason Nocturnus)
EventBot requesting permissions (Cybereason Nocturnus)Still in development but already a threat
Although it is currently in its early stages of development, EventBot can become a major Android malware threat since it is already capable of targeting hundreds of financial apps and the developers add more new feature in each version like encryption, dynamic library loading, and automatic adjustment to device models and locales.
Because the threat actor behind this malware updates it every few days, it's just a matter of time until it catches up to other highly dangerous Android trojans like Cerberus, Anubis, and xHelper.
For instance, EventBot's developers added a layer of obfuscation in the latest version, "perhaps taking the malware one step closer to being fully operational," according to the researchers.
To defend against an EventBot infection you should avoid third-party marketplaces if possible and always install apps only from the Google Play Store as they go through a vetting process that makes sure that most potentially malicious apps are rejected.
"Cybereason believes EventBot could be the next influential mobile malware because of the time the developer has already invested into creating the code and the level of sophistication and capabilities is really high," Cybereason Head of Threat Research Assaf Dahan said.
"By accessing and stealing this data, Eventbot has the potential to access key business data, including financial data. Mobile malware is no laughing matter and it is a significant risk for organizations and consumers alike."
EventBot indicators of compromise (IOCs) including malware sample hashes, and IP addresses and domains of its command and control servers, are available at the end of Cybereason Nocturnus' report.
Starting last month, the TrickBot gang has also begun using a malicious Android app dubbed TrickMo that steals transaction authentication numbers (TANs) — including one-time passwords (OTP), mobile TAN (mTAN), and pushTAN authentication codes — to bypass the 2FA protection used by various banks
No comments:
Post a Comment