James Shepperd23 Mar 2020
Home office is where the heart is…
Or is it… home office is where the hurt is?
Usually I am quite happy to have home office, in my division at ESET (IT company) we are permitted two per month. It’s not a lot but maybe that is why I look forward to it. My kids are at school, my wife is at work and my colleagues are behind a virtual wall that I control! (-;
Or, I should probably say, that was home office. With COVID-19 restrictions in place, home office has… certainly changed, a lot! For starters, both my kids and wife are home. Then, my team… well it just got a lot bigger. The number of ESET staff and departments I connect with has virtually multiplied by a factor of three, at least it feels like it. It’s not that I am bitter, just well, its not fun and games anymore.
VPN
Shields up! With only 2 home offices per month, I simply relied on my company provided Virtual Privacy Network (VPN) as a significant enough safeguard, but after reading this
blog on home office security measures end to end, which I requested; I took a look at my
router settings. Oh, looks like I have some security improvements to make. Anyway, with my VPN turned on I can access some otherwise restricted marketing resources, which have their own protection protocols. In simply terms a VPN lets you to make a secure connection to another network over the Internet, access region or security-restricted websites, shield your browsing activity. Now that I, along with every other marketer in the company is accessing these files from their home networks I can see why there is the added layer of protection.
Passwords
Best Practice Aside from the little notebook with the hard copy of passwords I keep buried under my..., I use a password manager, which can store all my needed credentials in one place, under one “master password”. Just as a reminder, create a strong password or
passphrase, keep the password(s) secure and consider a second (factor) method of protection that helps prevent unwanted access.
Even strong passwords can fall victim to malicious actors using
keyloggers and other technology to crack your online accounts. So, strongly consider using a product like
ESET Smart Security Premium that integrates several privacy protection features including password management and protection against keylogging via
Two Factor Authentication (2FA).
Two Factor Authentication
“Open Sesame” and… While my VPN is a prerequisite for accessing our intranet and a number of applications that can be found there, for more sensitive applications I am challenged at the “gate”. What I mean is that my login is quickly followed by a request for a single time passcode.
The companion app for our intranet platform pings my mobile phone with the authenticator, I enter the code and “I’m in!”. When I first came to the company, I used to mutter under my breath about accessing various admin dashboards or restricted forums with 2FA. I saw it as just another barrier or headache. But in the years since, especially working on our offer for small and medium businesses and small or home office clients I have seen up close how social media or whole websites get disrupted, events that cause serious reputational damage. I don’t want that kind of damage on my name. These days I even use 2FA on my personal email account after it got hacked.
Kids and Home Office
The Pain, now on to a more personal note, my kids interfering with my perfect home office vibe! The Corona virus has upped the ante on my multitasking skills. My kids have to learn – my wife and I are their new substitute teachers. We also have to work. So it means, teach and work at the same time. So, my top tip, keep them on their usual schedule.
Mornings: Wake at 6:30 am, we have a bite to eat and then put on our masks and glasses and then take a brisk 20min walk through the park behind our house. This gets everyone going and ready to start their daily assignments, which come via email. I know many of you won’t have empty parks behind your houses, but if you have an area near bye with low numbers of people (at 6:45-7:00 am they should be empty), then the benefit to mood and focus is (to me) worth the risk.
By 8:00 am, I am at my desk, and the kids have started with any assignments. Our rule is that they have to finish their first block of assignments by 11:00 am, the lunch time I had pre-COVID-19. I found that by addressing my needs first I am able to be more patient and adaptable with covering their needs.
Meals, well… when I shop, I buy a lot of fruit for snacks and when making sandwiches or cooking warm meals have started making double portions to ensure we have enough leftovers. They are starting to accept that we aren’t going to the store so often and they will get leftovers at least once every day. Smiley (-:
Afternoons: After lunch, I disengage from my work and review any questions, lost assignments, or missing workbook issues. Before sinking myself into that task I make sure to lock my PC (Ctrl+Alt+Del). That prevents my kids from accidentally loosing my work… or publishing anything to the company’s social media.
My wife: She has a busy job, lots of calls, video chats etc. This is a challenge. Back to my 8:00am – 11:00am sprint. During those hours he tries to be available for the kids, in the afternoon I am up. This trade off doesn’t mean we are in full teacher mode, but it allows one of us to accept a period of interruption, knowing that later, we will have higher quality work time. When we both know we’ll be engaged on conference calls or whatever… that is when some scheduled online educational games and snacks come in handy.

Oh, and the daily device wipe down: Since my hands haven’t completely fallen off, yet…
I also take the opportunity to wipe down my keyboard, mouse and trackpad. If you’ve got tablets, I’d do those to with (screen safe) cleaner or in a pinch simply a damp rag. I start with our devices and move on to doorknobs and high traffic surfaces.
Promises: I promised this personal view on my secure home office to the Public Relations team at ESET. After saying “YES”, I started to feel vulnerable. “My security practices are gonna be visible to all my colleagues and the wider public.” But, there is hope.
Only via critique can you learn better practices and maybe the Corona virus can achieve what GDPR and countless internet security awareness campaigns have yet to do, raise people’s appreciation for basic security measures.
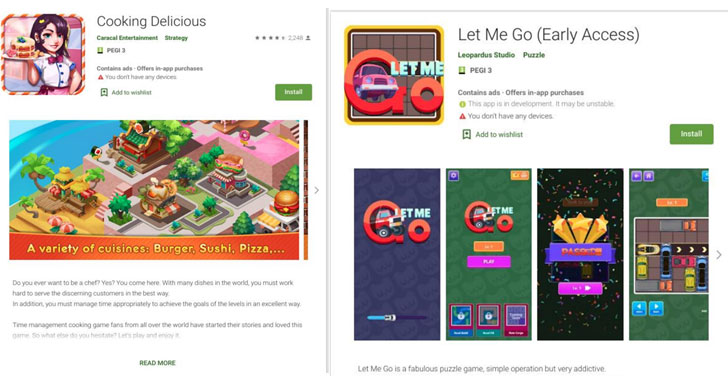
 (Image credit: Malwarebytes)
(Image credit: Malwarebytes)