 By Hack Unamatata 16 Απριλίου 2020, 21:11
By Hack Unamatata 16 Απριλίου 2020, 21:11Η hacking ομάδα Anonymous Global Hackers Crew σε πρώτη αποκλειστική συνέντευξη στο SecNews παρουσιάζει την δική της οπτική για την (αν)ασφάλεια στο διαδίκτυο. Ο Anon, ένας από τους τέσσερις ιδρυτές του Global Hackers Crew μιλάει για την ιστορία της hacking ομάδας, τους δεσμούς που ενώνουν τα μέλη της, τον πόλεμο που δέχονται από τα Μέσα Μαζικής Ενημέρωσης και τις κυβερνήσεις, τις hacking εκστρατείες και τους στόχους τους, μείζονα θέματα επικαιρότητας όπως η πανδημία COVID-19 και πολλά άλλα.
Αυτοαποκαλούνται “cyber vigilantes” (ήρωες-τιμωροί) αλλά και hacktivists καθώς κύριος στόχος της δουλειάς τους είναι το κοινό καλό. Σύμφωνα με τον Anon «είναι υπέροχο να ξυπνάμε τους ανθρώπους και στόχος μας είναι να απελευθερώσουμε τις μάζες από την προπαγάνδα»
Η Anonymous Global Hackers Crew ομάδα αποτελείται από έμπειρους hackers, κάθε ηλικίας, με εξαιρετικές ικανότητες πάνω στον προγραμματισμό, το coding, Password guessing και cracking, session hijacking, session spoofing, network traffic sniffing, denial of Service attacks, exploiting buffer overflow vulnerabilities, SQL injection και άλλα.

Πως ξεκίνησαν οι Global Hackers Crew;
Οι Global Hackers Crew «δημιουργήθηκαν τυχαία», σύμφωνα με τον Anon.
«Ασχολούμαι με το hacking από το 93’-94’ κάνοντας παράλληλα και άλλα πράγματα γύρω από τους Η/Υ όπως το να τρέχω το δικό μου σύστημα με bots. Τότε γράφαμε κώδικα σε βάρδιες οπότε στο διάλλειμά μου έβλεπα τηλεόραση. Μια μέρα, σε κάποιο διάλειμμα μου έπεσα πάνω σε μια διαφήμιση για ένα site με webcam shows για ενήλικους. Από περιέργεια, το επισκέφτηκα χωρίς να γνωρίζω ακριβώς τι έκανα και άλλαζα συνεχώς «δωμάτια». Εκεί γνώρισα κάποια, που στην συνέχεια, έγινε η κοπέλα μου και μου έδειξε μια διαφορετική πλευρά αυτού του site», αναφέρει ο hacker. Στο συγκεκριμένο site γνωριμιών συνέβαιναν παράνομα πράγματα στο παρασκήνιο. Ο Anon θέλησε να ξεσκεπάσει τους διαχειριστές της ιστοσελίδας για τις ανήθικες δραστηριότητες τους.
«Έτσι, ξεκίνησα έναν μικρό πόλεμο με τα αφεντικά αυτής της εταιρείας και τυχαία ενώ πήγαινα να συναντήσω την κοπέλα μου, γνώρισα κάποιον στο λεωφορείο που ήταν και αυτός hacker με τον οποίον δεθήκαμε και, στη συνέχεια, έγινε ένα από τα ιδρυτικά μέλη των Global Hackers Crew,» τονίζει ο Anon. Στα ιδρυτικά μέλη προστέθηκαν και δύο ακόμη φίλοι των δύο hackers.
Με αυτόν τον τρόπο βρέθηκαν μαζί οι τέσσερις ιδρυτές των Global Hackers Crew. Με τον καιρό, η ομάδα μεγάλωνε καθώς όλο και περισσότεροι άνθρωποι ήθελαν να συμμετάσχουν στις επιχειρήσεις τους. «Δρούμε για το καλό των ανθρώπων, προειδοποιώντας τους για τους online κινδύνους όπως οι διαρροές ασφαλείας, κάτι που συνέβη πρόσφατα με το Zoom..» τονίζει ο hacker.
Οι Global Hackers Crew εντάχθηκαν στους Anonymous επειδή εντόπισαν πολλά κοινά στις επιχειρήσεις τους.

Οι Anonymous είναι μια αποκεντρωμένη διεθνής hacktivist ομάδα που είναι ευρέως γνωστή για τις διάφορες κυβερνοεπιθέσεις εναντίον πολλών κυβερνήσεων, κυβερνητικών θεσμών και κυβερνητικών υπηρεσιών και εταιρειών.
Οι Anonymous δημιουργήθηκαν το 2003 στο imageboard 4chan που αντιπροσωπεύει την έννοια πολλών χρηστών της κοινότητας στο διαδίκτυο αλλά και στη πραγματική ζωή που ταυτόχρονα υπήρχαν ως αναρχικοί. Τα ανώνυμα μέλη μπορούν να διακριθούν δημόσια από τη χρήση μάσκας Guy Fawkes στο στυλ που απεικονίζεται στο γραφικό μυθιστόρημα και την ταινία V for Vendetta. Ωστόσο, αυτό μπορεί να μην συμβαίνει πάντα, καθώς ορισμένα από τα μέλη προτιμούν να καλύπτουν το πρόσωπό τους χωρίς να χρησιμοποιούν τη γνωστή μάσκα ως μεταμφίεση. Μερικοί Anonymous επιλέγουν επίσης να καλύψουν τις φωνές τους μέσω των προγραμμάτων αλλοίωσης φωνής.

Παρακολουθήστε όλη την συνέντευξη των Anonymous Global Hackers Crew στο Youtube channel του SecNews και αν επιθυμείτε να μάθετε ακόμα περισσότερα για την δράση των hackers επισκεφθείτε το YouTube channel τους και το Twitter account τους.


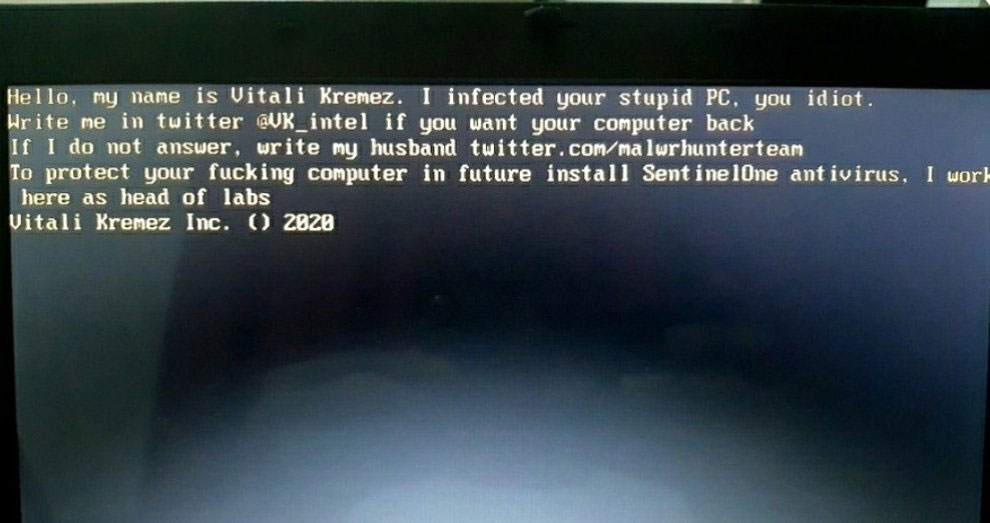 MBR locker impersonating Vitali and MalwareHunterTeam
MBR locker impersonating Vitali and MalwareHunterTeam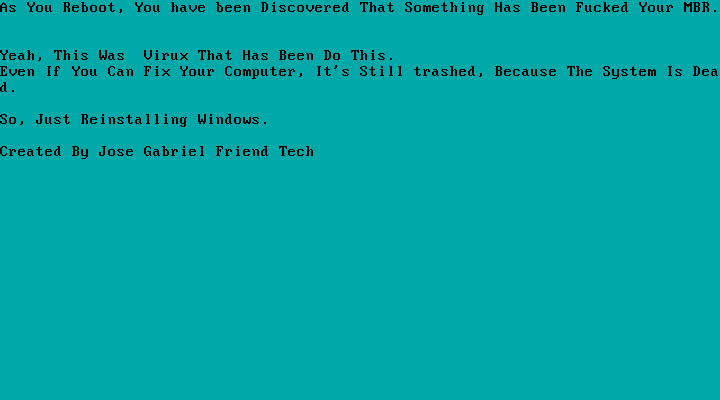 Example of recent MBRLocker
Example of recent MBRLocker



