By Sergiu Gatlan March 23, 2020 07:12 PM 0

Sites promoting a bogus Corona Antivirus are taking advantage of the current COVID-19 pandemic to promote and distribute a malicious payload that will infect the target's computer with the BlackNET RAT and add it to a botnet.
The two sites promoting the fake antivirus software can be found at antivirus-covid19[.]site and corona-antivirus[.]com as discovered by the Malwarebytes Threat Intelligence team and researchers at MalwareHunterTeam, respectively.
While the former was already taken down since Malwarebytes' report, the one spotted by MalwareHunterTeam is still active but it had its contents altered, with the malicious links removed and a donation link added to support the scammers' efforts — spoiler alert, no donations were made until now.
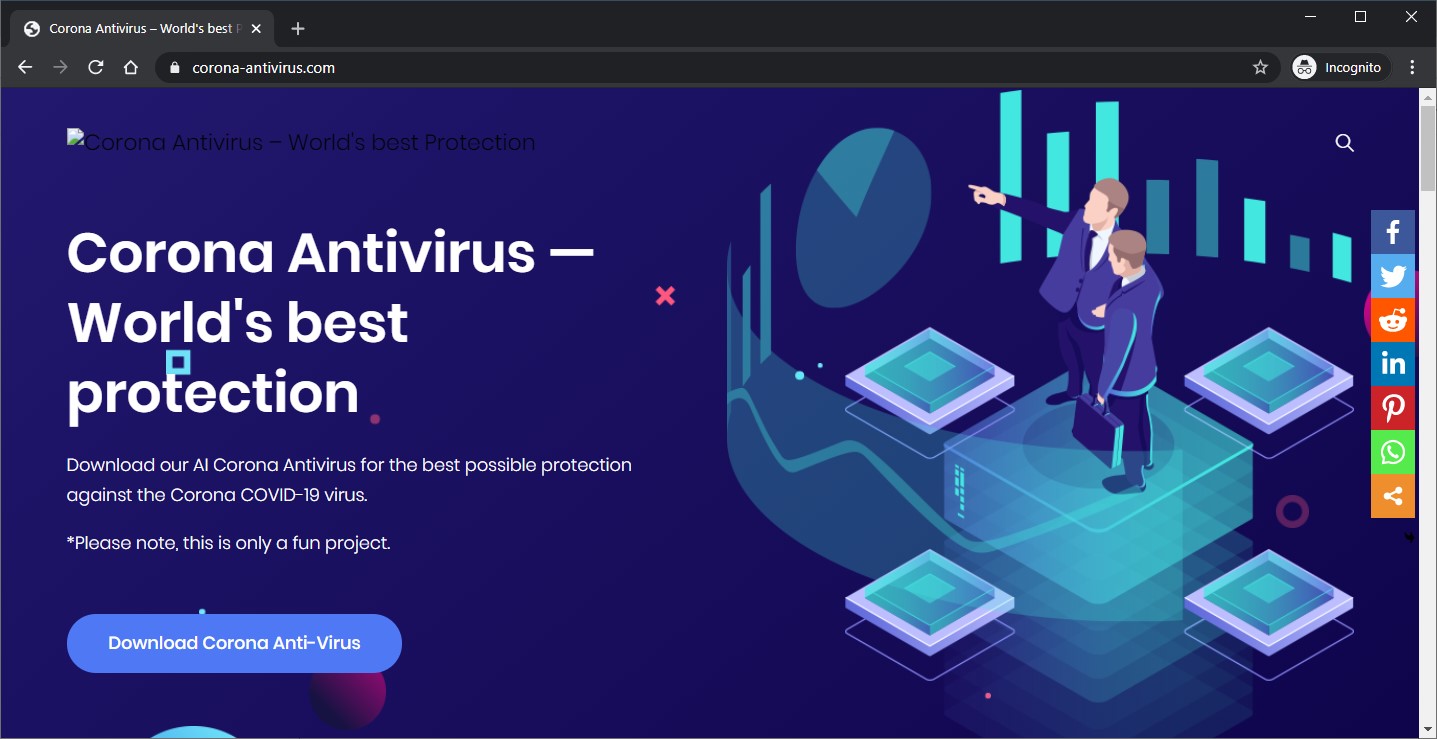
"Download our AI Corona Antivirus for the best possible protection against the Corona COVID-19 virus," the site reads. "Our scientists from Harvard University have been working on a special AI development to combat the virus using a mobile phone app.
Last but not least, the malicious sites' makers also mention an update that will add VR sync capabilities to their fake antivirus: "We analyse the corona virus in our laboratory to keep the app always up to date! Soon a corona antivirus VR synchronization will be implemented!"
If anyone would fall this, they would end up downloading an installer from antivirus-covid19[.]site/update.exe (link is now down) that will deploy the BlackNET malware onto their systems if launched.
BlackNET will add the infected device to a botnet that can be controlled by its operators:
• to launch DDoS attacks
• to upload files onto the compromised machine
• to execute scripts
• to take screenshots
• to harvest keystrokes using a built-in keylogger (LimeLogger)
• to steal bitcoin wallets
• to harvest browser cookies and passwords.
The BlackNET RAT, which was rated as 'skidware malware' by MalwareHunterTeam, is also capable to detect if it's being analyzed within a VM and it will check for the presence of analysis tools commonly used by malware researchers, per c0d3inj3cT's analysis.
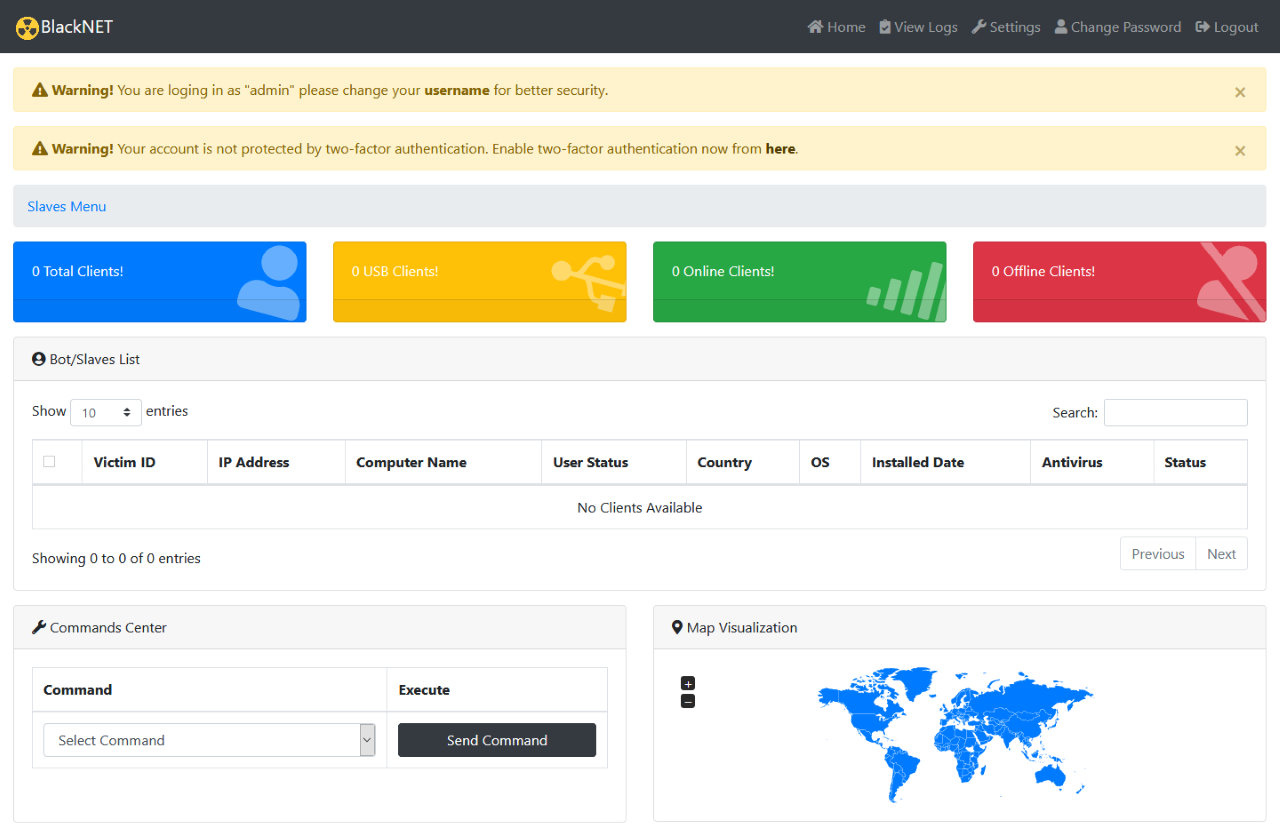 BlackNET command panel
BlackNET command panelThe malware also comes with bot management features including restarting and shutting down the infected devices, uninstalling or updating the bot client, and opening visible or hidden web pages.
One of the sites promoting this bogus Corona Antivirus was spotted by MalwareHunterTeam on March 6, while the other was exposed by Malwarebytes' Threat Intelligence team in a report published today.
In somewhat related news, an HHS.gov open redirect is currently abused by attackers to deliver Raccoon info-stealing malware payloads onto targets' systems via a coronavirus-themed phishing campaign.
The actors behind these ongoing phishing attacks use the open redirect to link to a malicious attachment that delivers a VBS script previously spotted while being employed by the operators behind Netwalker Ransomware to deploy their payloads.
The World Health Organization (WHO), the U.S. Cybersecurity and Infrastructure Security Agency (CISA), and the U.S. Federal Trade Commission (FTC) have all warned about Coronavirus-themed phishing and attacks targeting potential victims from countries around the globe (1, 2, 3).
No comments:
Post a Comment