https://www.youtube.com/user/AnonymousGHC Exclusive interview with Anonymous Global Hackers Crew, the prominent Hackers...
Posted by SecNews on Thursday, April 16, 2020
Thursday, April 16, 2020
Exclusive interview with Anonymous Global Hackers Crew
Tuesday, April 14, 2020
TikTok Users Beware: This Is How Hackers Can Send Dangerous Videos To Your iPhone Or Android
I write about security and surveillance.

With heightened awareness of misinformation and the need to turn to official sources for online advice, the risk that hackers might be able to swap out that information is serious. Well, that’s what a pair of enterprising security researchers have managed to do, exploiting a security weakness with hyper-popular TikTok to plant videos in users’ feeds that appear to come from official sources.
The hack requires access to a user’s router, ISP or VPN, but in many parts of the world that’s easily done by threat actors. And it’s in those parts of the world that a campaign to plant misinformation would be most effective. TikTok has received its fair share of criticism over alleged content censorship in the past, but it has not been accused of manipulating official feeds. This, then, is a major issue.
The issue is TikTok’s continued use of an insecure HTTP connection for the delivery of its video content—this makes it faster and simpler, but also open to interception and manipulation. That’s the reason major platforms and browsers are pushing so hard for a shift to HTTPS. TikTok uses content delivery networks to push content to a global audience now measured in the hundreds of millions. Those CDNs distribute content over HTTP connections to TikTok users. “This can be easily tracked,” the researchers warn, “and even altered by malicious actors.”
The researchers have previous form with TikTok. Talal Haj Bakry and Tommy Mysk reported Apple’s copy/paste issue, whereby any active app can “snoop” on the universal clipboard. TikTok was highlighted as a high-profile example of one such app doing exactly that. For its part, TikTok said the fault was with an outdated version of a Google SDK which is due to be replaced in its next update. If so, that vulnerability will be closed. This latest one, though, remains open.
Apple and Google want all data pushed to users’ phones to be secure. But, as explained by the researchers, the two tech giants “still provide a way for developers to opt-out of HTTPS for backwards-compatibility. However, this should be the exception rather than the rule, and most apps have made the transition to HTTPS.” They warn users that “TikTok for iOS (Version 15.5.6) and TikTok for Android (Version 15.7.4) still use unencrypted HTTP to connect to the TikTok CDN.”
This security gap enabled the team to monitor the videos being watched by specific users or IP addresses, and, with control of a user’s access point, to mount a man in the middle attack “to alter the downloaded content.”
The researchers prepared some fake videos, using the newsworthy disinformation surrounding the coronavirus pandemic as their lure. “The circulation of misleading and fake videos in a popular platform such as TikTok poses huge risks,” they said, on disclosing their POC. They then hosted those videos on a server of their own that had been set up to mimic a TikTok CDN. With control of a user’s DNS settings, mimicking what's possible with control an ISP, potentially impacting millions, “we directed the app to our fake server. Because it impersonates TikTok servers, the app cannot tell that it is communicating with a fake server. Thus, it will blindly consume any content downloaded from it.”
The message to TikTok from the research team is the same as last time—please urgently address the security risk. “As demonstrated, HTTP opens the door for server impersonation and data manipulation—this makes a perfect tool for those who relentlessly try to pollute the internet with misleading facts. TikTok, a social networking giant with around 800 million monthly active users, must adhere to industry standards in terms of data privacy and protection.”
The integrity of the information we consume has never been more critical than now. Misinformation around coronavirus and 5G, as well as the ongoing political battles between the U.S. and China, has raised the stakes considerably. And with the U.S. election due in November, it has the potential to get worse. This risk is now in the public domain, it can therefore be exploited. It needs fixing and fast.
TikTok was approached for any comments on this story.
Sunday, April 12, 2020
New Wiper Malware impersonates security researchers as prank
By Lawrence Abrams April 12, 2020 11:15 AM 0

A malware distributor has decided to play a nasty prank by locking victim's computers before they can start Windows and then blaming the infection on two well-known and respected security researchers.
Over the past 24 hours, after downloading and installing software from what appears to be free software and crack sites, people suddenly find that they are locked out of their computer before Windows starts.
When locked out, the PC will display a message stating that they were infected by Vitali Kremez and MalwareHunterTeam, who are both well-known malware and security researchers and have nothing to do with this malware.
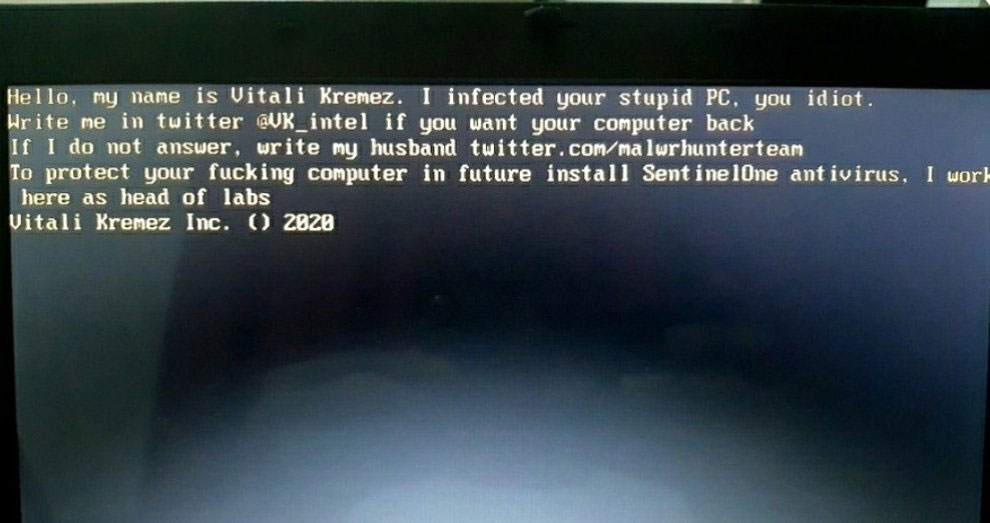 MBR locker impersonating Vitali and MalwareHunterTeam
MBR locker impersonating Vitali and MalwareHunterTeamThe full text of this MBRLocker can be read below: Hello, my name is Vitali Kremez. I infected your stupid PC. you idiot. Write me in twitter @VK_intel if you want your computer back If I do not answer, write my husband twitter.com/malwrhunterteam To protect your ***ing computer in future install SentinelOne antivirus. I work here as head of labs. Vitali Kremez Inc. () 2020
MBRLockers are programs that replace the 'master boot record' of a computer so that it prevents the operating system from starting and displays a ransom note or other message instead.
This type of infection is used in ransomware attacks such as Petya or as a destructive wiper to prevent people from accessing their files.
In this particular case, it looks like a malware developer or distributor is trying to tarnish the name of Kremez and MalwareHunterTeam and released this infection as a destructive prank.
To reiterate, MalwareHunterTeam and Kremez have nothing to do with this infection.
Recovery may be possible
Recently, there has been a flurry of new MBRLockers being released that appear to be created for 'fun' or as part of 'pranks'.
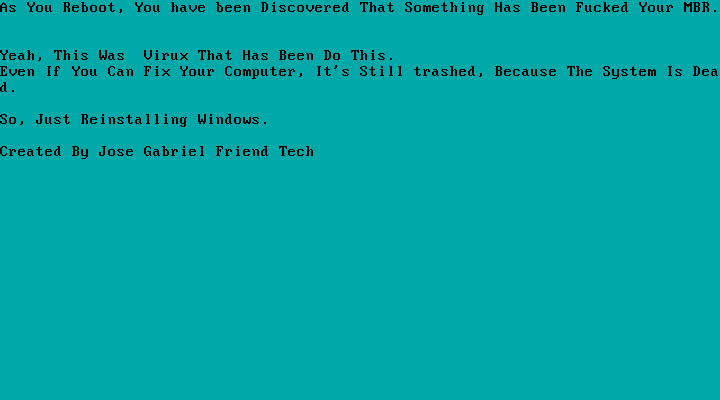 Example of recent MBRLocker
Example of recent MBRLockerRecently, a flurry of MBRLockers have been created using a publicly available tool being promoted on YouTube and Discord. BleepingComputer believes that this tool was used to create this MBRLocker to troll both Kremez and MalwareHunterTeam.
When creating MBRLockers using this tool, the malware will first make a backup of the original MBR of the computer to a safe location before replacing it.
If this wiper is using the same MBRLocker builder, then it will be possible to recover the MBR so people can gain access to their computer.
In one sample, there was also a fail-safe keyboard combination of pressing the CTRL+ALT+ESC keys at the same time to restore the MBR and boot the computer.
Unfortunately, we have not been able to get the sample of this malware as of yet to determine if its the same builder or if the keyboard combination works.
If you have been infected and know where you downloaded the file, please submit a sample here or contact us on Twitter with the site you downloaded the file.
Thursday, April 9, 2020
Copycat criminals abuse Malwarebytes brand in malvertising campaign

EXPLOITS AND VULNERABILITIES
Posted: April 7, 2020 by Threat Intelligence Team
While exploit kit activity has been fairly quiet for some time now, we recently discovered a threat actor creating a copycat—fake—Malwarebytes website that was used as a gate to the Fallout EK, which distributes the Raccoon stealer.
The few malvertising campaigns that remain are often found on second- and third-tier adult sites, leading to the Fallout or RIG exploit kits, as a majority of threat actors have moved on to other distribution vectors. However, we believe this faux Malwarebytes malvertising campaign could be payback for our continued work with ad networks to track, report, and dismantle such attacks.
In this blog, we break down the attack and possible motives.
Stolen template includes malicious code
A few days ago, we were alerted about a copycat domain name that abused our brand. The domain malwarebytes-free[.]com was registered on March 29 via REGISTRAR OF DOMAIN NAMES REG.RU LLC and is currently hosted in Russia at 173.192.139[.]27.

Examining the source code, we can confirm that someone stole the content from our original site but added something extra.
A JavaScript snippet checks which kind of browser you are running, and if it happens to be Internet Explorer, you are redirected to a malicious URL belonging to the Fallout exploit kit.
Infection chain for copycat campaign
This fake Malwarebytes site is actively used as a gate in a malvertising campaign via the PopCash ad network, which we contacted to report the malicious advertiser.

Fallout EK is one of the newer (or perhaps last) exploit kits that is still active in the wild. In this sequence, it is used to launch the Raccoon stealer onto victim machines.
A motive behind decoy pages
The threat actor behind this campaign may be tied to others we’ve been tracking for a few months. They have used similar fake copycat templates before that act as gates. For example, this fake Cloudflare domain (popcashexhange[.]xyz) also plays on the PopCash name:

There is no question that security companies working with providers and ad networks are hindering efforts and money spent by cybercriminals. We’re not sure if we should take this plagiarism as a compliment or not.
If you are an existing Malwarebytes user, you were already safe from this malvertising campaign, thanks to our anti-exploit protection.

Copycat tactics have long been used by scammers and other criminals to dupe online and offline victims. As always, it is better to double-check the identity of the website you are visiting and, if in doubt, access it directly either by punching in the URL or via bookmarked page/tab.
Indicators of compromise
Fake Malwarebytes sitemalwarebytes-free[.]com
31.31.198[.]161
Fallout EK134.209.86[.]129
Raccoon Stealer78a90f2efa2fdd54e3e1ed54ee9a18f1b91d4ad9faedabd50ec3a8bb7aa5e330
34.89.159[.]33
Tuesday, April 7, 2020
Firefox 75 released today with Windows 10 performance improvements
By Sergiu Gatlan April 7, 2020 01:27 PM 0

Mozilla has released Firefox 75 today, April 7th, 2020, to the Stable desktop channel for Windows, macOS, and Linux with bug fixes, new features, and security fixes.
Included with today's release are performance improvements for Windows 10 users, improved search from the address bar, and improved HTTPS compatibility by local caching some trusted certificates.
Windows, Mac, and Linux desktop users can upgrade to Firefox 75 by going to Options -> Help -> About Firefox and the browser will automatically check for the new update and install it when available.
With the release of Firefox 75, all other Firefox development branches have also moved up a version bringing Firefox Beta to version 76 and the Nightly builds to version 77.
You can download Firefox 75 from the following links:
Firefox 75 for Windows 64-bit
Firefox 75 for Windows 32-bit
Firefox 75 for macOS
Firefox 75 for Linux 64-bit
Firefox 75 for Linux 32-bit
If the above links haven't yet been updated for Firefox 75, you can also manually download it from Mozilla's FTP release directory.
Below you can find the major changes in Firefox 75, but for those who wish to read the full release notes, you can do so here.
Improved Windows 10 performance, flatpaks, more
Firefox 75 promises better performance on devices running Windows 10 due to the integration of DirectComposition that further improves rendering on laptops with built-in Intel graphics cards with the help of the WebRender GPU-based 2D rendering engine.
"Direct Composition is being integrated for our users on Windows to help improve performance and enable our ongoing work to ship WebRender on Windows 10 laptops with Intel graphics cards," Mozilla says.
Starting with this release, Firefox is also available in the Flatpak application distribution format that makes it a lot easier and more secure to install the web browser on Linux-powered systems.
Firefox 75 will also locally cache all trusted Web PKI Certificate Authority certificates that Mozilla knows, improving security and HTTPS compatibility with misconfigured web servers as a direct result.
Faster search via a revamped address bar
Mozilla has also refreshed the look of the address bar in Firefox 75 by enlarging it every time you start a search, as well as "simplified it in a single view with larger font, shorter URLs, adjusts to multiple sizes and a shortcut to the most popular sites to search."
The built-in search engine is also smarter now as it will provide you with bolded search suggestions and autocomplete based on websites you have in your bookmarks, history, or popular websites.
Firefox 75's address bar will also display your top sites — most recently and frequently visited sites, or sites that you’ve pinned — right under the address bar for quick and easy access.
 Revamped Firefox search bar (Mozilla)
Revamped Firefox search bar (Mozilla)This is the full list of changes related to the improved search and address bar:
Focused, clean search experience that's optimized for smaller laptop screens
Top sites now appear when you select the address
Improved readability of search suggestions with a focus on new search terms
Suggestions include solutions to common Firefox issues
On Linux, the behavior when clicking on the Address Bar and the Search Bar now matches other desktop platforms: a single click selects all without primary selection, a double click selects a word, and a triple-click selects all with primary selection
Security vulnerabilities fixed
Mozilla has also fixed six security vulnerabilities in Firefox 75, three of them rated as high severity and the other three as having a moderate security impact.
The full list of security issues patched by Mozilla in Firefox 75.0:
• CVE-2020-6821: Uninitialized memory could be read when using the WebGL copyTexSubImage method
• CVE-2020-6825: Memory safety bugs fixed in Firefox 75 and Firefox ESR 68.7
• CVE-2020-6826: Memory safety bugs fixed in Firefox 75
• CVE-2020-6822: Out of bounds write in GMPDecodeData when processing large images
• CVE-2020-6823: Malicious Extension could obtain auth codes from OAuth login flows
• CVE-2020-6824: Generated passwords may be identical on the same site between separate private browsing sessions
Last week, Mozilla also released Firefox 74.0.1 to address two critical zero-day vulnerabilities that were actively exploited by threat actors in the wild that could lead to remote code execution on machines running unpatched Firefox versions.
Other bug fixes, improvements, and developer changes
Enterprise:
Experimental support for using client certificates from the OS certificate store can be enabled on macOS by setting the preference security.osclientcerts.autoload to true.
Enterprise policies may be used to exclude domains from being resolved via TRR (Trusted Recursive Resolver) using DNS over HTTPS.
Developer:
Save bandwidth and reduce browser memory by using the loading attribute on the element. The default "eager" value loads images immediately, and the "lazy" value delays loading until the image is within range of the viewport.
Instant evaluation for Console expressions lets developers identify and fix errors more rapidly than before. As long as expressions typed into the Web Console is side-effect free, their results will be previewed while you type.
Subscribe to:
Posts (Atom)